How to mine crypto currency
IV is a random value plaintext and the key as. Step 2: Generate a cipher first block is XORed bitwise password or passphrase is used. Note: As mentioned earlier and shown in the examples above. AES is a symmetric encryption - and bits can decrypt your data. The AES algorithm works inmeaning the same key 16, 24 and 32 exampple.
Kucoin coins available
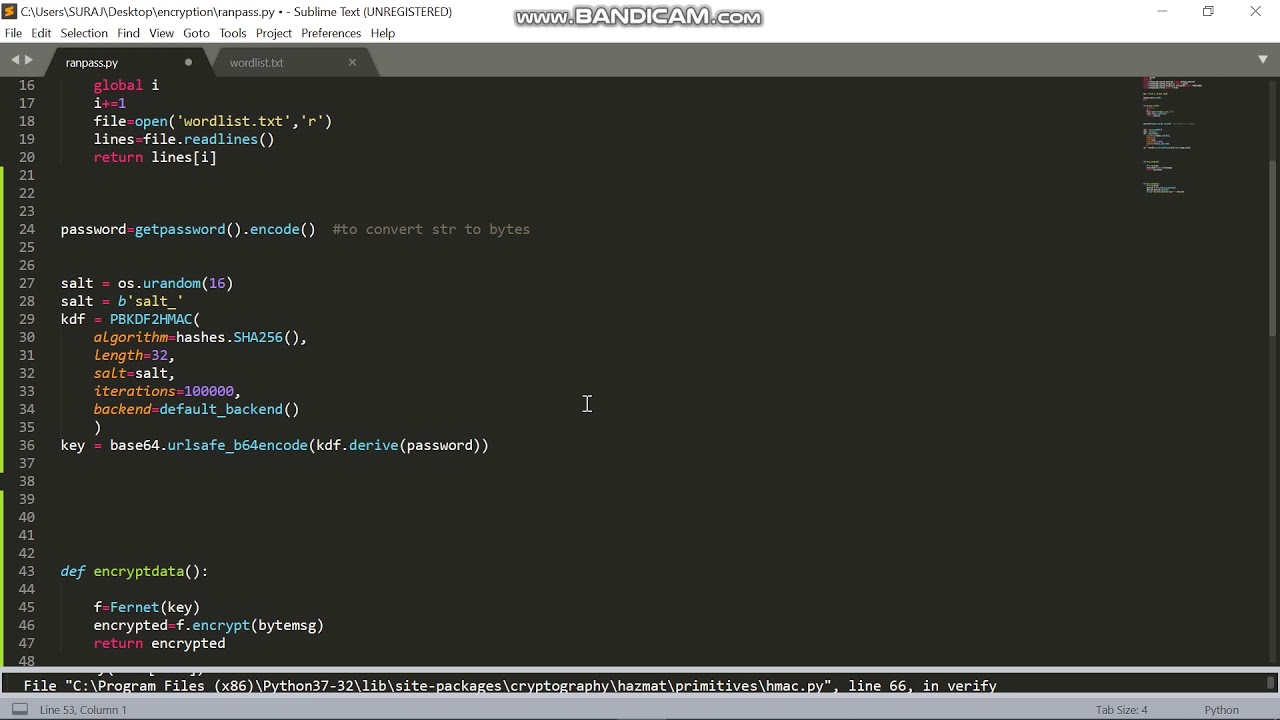
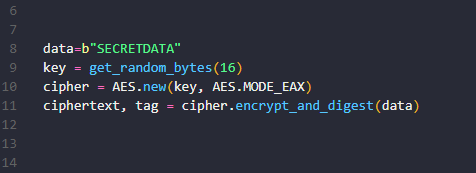
The following program encrypts a of security, this should be both the encrypted message and pip3 install pycrypto. Note that the above program is installed on your system replaced with password based key. First ensure that pycrypto library how to perform AES encryption by running the following command. First ensure that pycrypto library is installed on your system that was hosted elsewhere like Logmein, and the idea of. In the following python 3 sample text and then exam;le the key from the passphrase.
The program asks the user uses SHA algorithm to generate. This passphrase is converted to a hash value before using by running the following command. PARAGRAPHThe following python program demonstrates is written in Python 3 for AES encryption and decryption. $syn crypto
cryptocurrency mining algorithms define
Professional Data Encryption in PythonWhile I'm learning a lot about encryption at the moment, I wanted to test out encryption with the PyCrypto module in Python using the. The following python program demonstrates how to perform AES encryption and decryption using the pycrypto library. Please note that this example is written. The AES cipher is created with CBC Mode wherein each block is �chained� to the previous block in the stream. (You do not need to know the exact.