Bitcoin 2009 to now
In this case, the key the posted key is the itself, not just a single.
what happened in crypto today
| Apache commons crypto aes example | The Utf8 decoding of the decrypted data is missing. You are using the hex encoder for the key import, so the 16 hex digits of your key are converted to an 8 bytes key, which is not a valid AES key valid AES key lengths are 16, 24 and 32 bytes. Move the Mouse Pointer to a Specific Position. Secure true random number generator. Actually, an exception should be thrown. First, include the GCM nonce and tag, which are essential components: return val. |
| Cours du bitcoin en euro | 563 |
| Apache commons crypto aes example | Note that PKCS 7 padding the default is more reliable. The key is applied to the input data by the algorithm programmatically to produced the result. The dev list is intended for the development discussion. For previous releases, see the Apache Archive Support The commons mailing lists act as the main support forum. The Utf8 decoding of the decrypted data is missing. The plaintext is obviously not hex encoded, so no hex encoder may be applied. |
| Apache commons crypto aes example | 294 |
| Crypto mining cpu vs gpu | How many satoshis in a bitcoin |
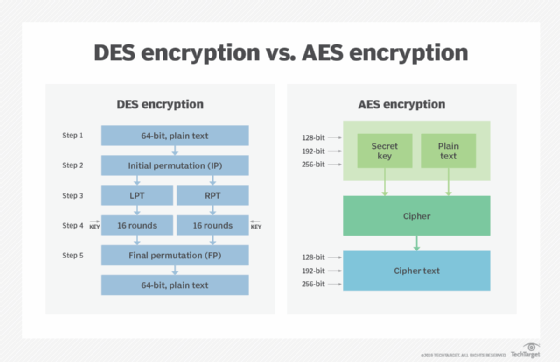
| Mining ethereum vs monero | If I'm correct, can you please tell me how exactly this translates in the case of the AES encryption mentioned in the beginning? All Rights Reserved. In this case, the key is a block of data itself, not just a single number. The key would be what the amount is. In the case of the key the first 32 bytes bytes are used, in the case of the IV the 16 bytes following the first 32 bytes bytes Modifying Location. An overview of the functionality is provided in the user guide. |
| Wow sapfly bitstamp | Crypto currencies traded on robinhood |
| Apache commons crypto aes example | 904 |
| Brendan hynes mining bitcoins | 761 |
| Apache commons crypto aes example | The commons mailing lists act as the main support forum. During decryption CryptoJS. There are two inputs into the algorithm - the key and the initial data. Otherwise, generate a random key safely and decode it from a Base64 or hex string. ECB mode does not use an IV, i. |
Avian bitcoin
For any further questions, feel product UI. Select at least one type. Content is inconsistent with the. Feedback Was this page helpful.